Regularly reviewing user permissions is important to reduce the risk of data overexposure and breaches. Overpermissioned users pose a significant security risk. Restricting access to only necessary information for individuals to perform their jobs can significantly reduce risk. By conducting regular permissions audits in Microsoft 365 and SharePoint, organizations can ensure that sensitive information access remains appropriate, safe and secure.
What is permissions auditing?
A permissions audit is the process of scanning your data repositories and systems (e.g., Microsoft 365, SharePoint, OneDrive) to identify the permissions granted to users and service accounts. This process creates a visual ‘permissions map’ or matrix of your organization’s digital environment and the permissions granted to each entity.
Why is permissions auditing important in Microsoft 365 and SharePoint?
Performing permissions audits is an effective way to decrease data risk by providing valuable insights into potential vulnerabilities and access control issues. If an employee has access to sensitive data that isn’t required for their job, it can increase the risk of data breaches if their account is compromised. Similarly, if an external application has access to more data than necessary, it can increase the risk of a breach through that application.
If you are migrating to M365 from SharePoint Server, permissions auditing is an important step, as the permissions will need to be replicated in your SharePoint Online environment. Plus, it gives you the opportunity to remediate any access issues prior to rolling out M365.
Permissions auditing in Microsoft 365 and SharePoint with NC Protect
Unfortunately, one of the biggest IT challenges is identifying who has access to what, how the permissions were granted and ensuring responsible access and data usage. That’s where third party solutions can be helpful.
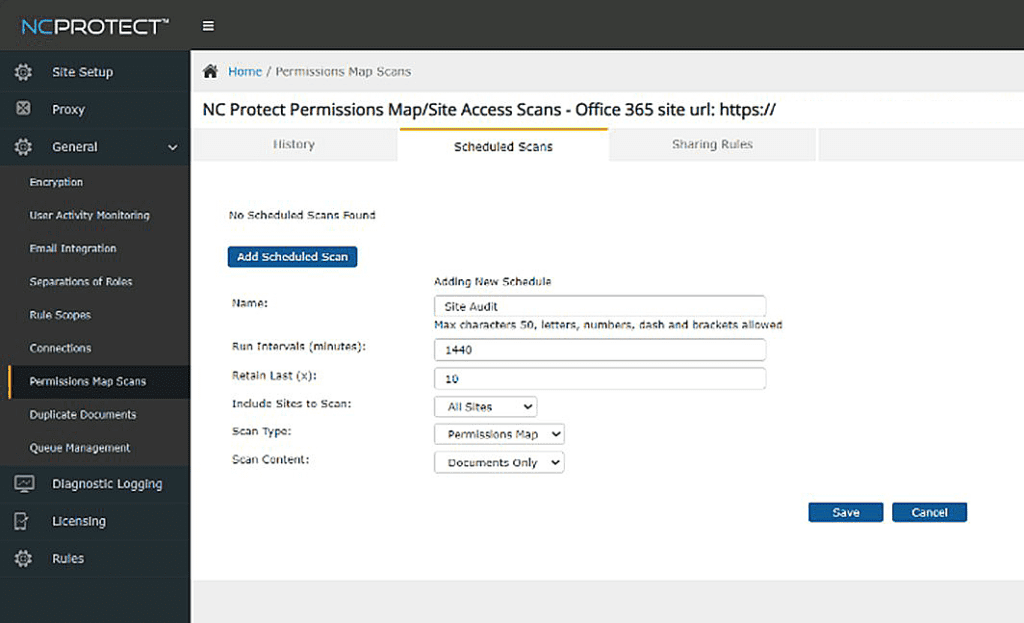
Effectively audit and manage permissions in M365, SharePoint on-premises and file shares with permissions map scanning from NC Protect. Run permissions map and site access scans to identify who has access to the content stored in SharePoint, OneDrive and file shares and help determine where permissions can be reduced. With NC Protect, easily identify which users have unnecessary permissions that could increase the risk of a data breach. You can then use these reports to rectify the oversharing of content within your tenant.
NC Protect’s built-in permissions map and site access scans can be run on demand or be scheduled at regular intervals to deliver detailed reports on:
- All sites users have access to and what permissions they have on these sites.
- Which users can access documents and items within one or multiple SharePoint lists and libraries.
- The level of permissions users and admins have to SharePoint Lists, Libraries and Sites.
- If the permissions are inherited or directly given to the user.
- Additionally, the audit log tool tracks access to individual documents and actions taken with the document by a user.
Once you review the results, NC Protect scans can be used to update individual user or group access using sharing rules to control access issues and oversharing.
Go beyond permissions scans with dynamic access control
While auditing permissions is important for risk management and compliance, enforcing governance is critical to prevent security incidents in the first place. NC Protect’s contextual attribute-based access control (ABAC) and data protection policies ensure that your organization’s governance and security rules are being enforced dynamically and consistently at the data layer. Combined with our permissions auditing and user activity logging, NC Protect provides a complete data-centric solution to ensure appropriate, least privileged access to your Microsoft 365, SharePoint and file share content.
Contact us for a demo.