Resource Center
Filter by Product
All Resources | Kojensi | NC Protect | Trusted Data Integration
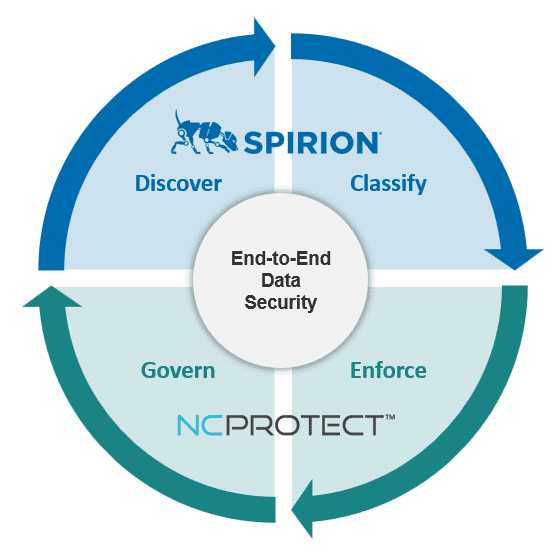
NC Protect & Spirion for End to End Data Security
NC Protect with Spirion delivers policy-driven, data-centric security that provides deep visibility into sensitive data, automatically discovering, classifying, and protecting it across Microsoft environments. They enable organizations to protect data and simplify compliance with dynamic, real-time, attribute-based control over how sensitive data is accessed, shared, and used.
FERPA Compliance in Higher Education: Controlling Access to Student Data.
Learn how universities can reduce FERPA risk by improving visibility into student records, strengthening access controls, and limiting oversharing across collaboration tools and endpoints.

End to End Data Lifecycle Management for Microsoft 365 & GCC High with Spirion and NC Protect
Discover, classify, and protect sensitive information with unparalleled precision using NC Protect and Spirion. Together, they offer a seamless solution that ensures your data remains visible and secure.
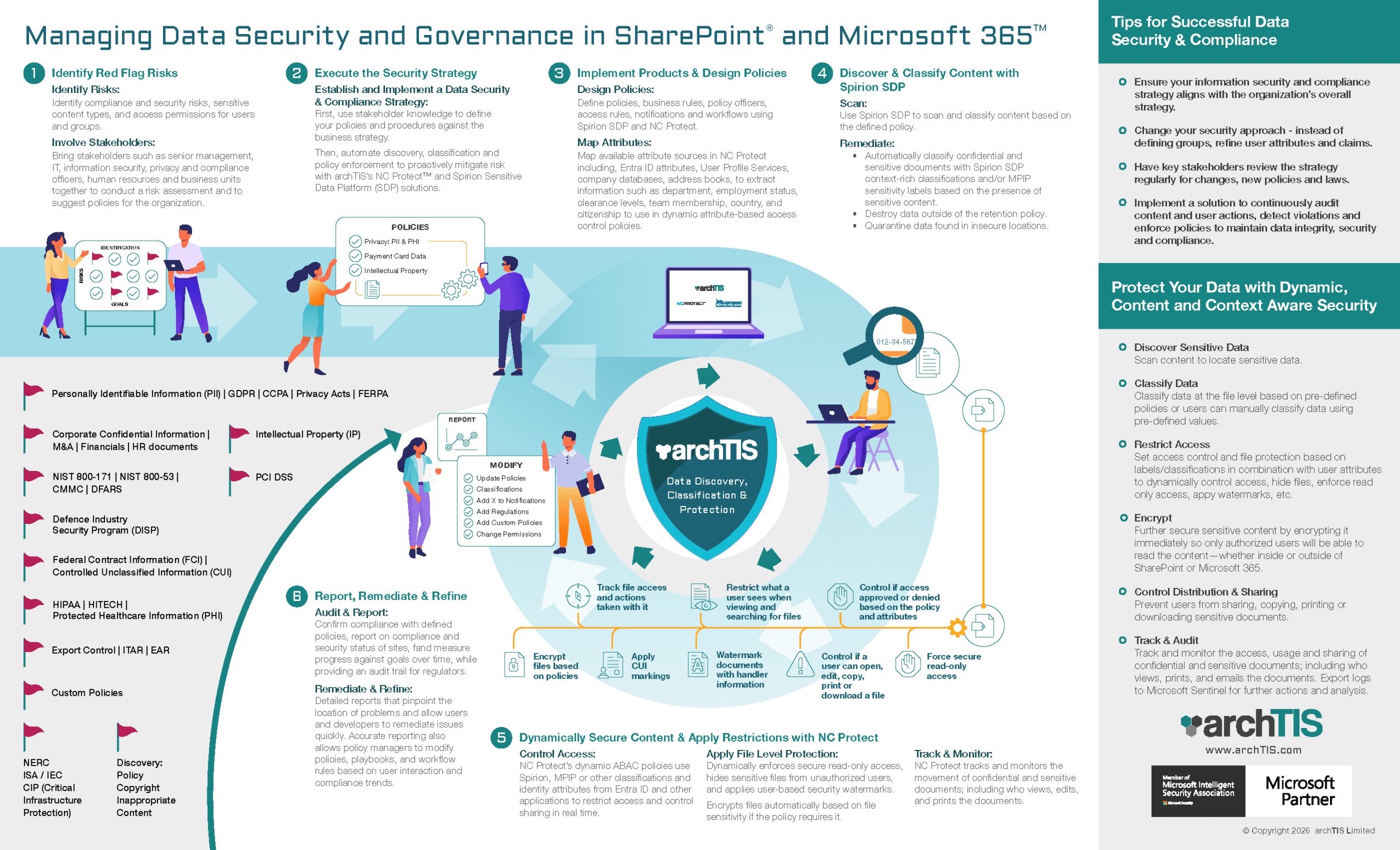
Managing Data Security and Governance in SharePoint and Microsoft 365 with NC Protect & Spirion
Discover how to protect your data in M365 with dynamic, content and context aware security. From accurate discovery and classification to policy-enforced access control and protection, archTIS solutions have you covered.
Tech Talk: Dynamically Securing File Sharing in Microsoft Teams with ABAC
Microsoft Teams makes collaboration easy, but it can also create security and compliance risks. Over-permissioned channels and accidental file sharing can expose sensitive data, turning everyday teamwork into unintended policy violations. This Tech Talk will show you practical ways to reduce risk without disrupting collaboration.

Data Sheet: NC Protect for Microsoft Teams
NC Protect for Microsoft 365 enables secure collaboration in Microsoft Teams without the overhead of complex user permissions, poorly applied at-rest encryption, or the need to create multiple channels to limit access to files. Learn more.

NC Protect for Microsoft 365 Technical Specifications
The following technical requirements represent the minimum recommended configuration for installing NC Protect for Microsoft 365 version 9.x. archTIS recognizes that each deployment is different and can advise on how your specific environment should be configured to ensure optimal performance.

CUI Compliance Checklist: Guide to Achieving CMMC & NIST 800-171 Compliance
Unlocking CUI compliance for CMMC and NIST doesn’t have to be overwhelming. Download this checklist to help you navigate the essential steps toward achieving compliance.

Trusted Data Integration Datasheet
archTIS Trusted Data Integration (TDI) is a lightweight, fast and agile solution to solve the problem of how to integrate, secure and govern sensitive and classified structured data at scale and speed.

Video: Simplify compliance and security with archTIS and Microsoft
Discover how NC Protect leverages Microsoft security investments to enhance information protection by adding dynamic ABAC policy-based access and data-centric controls to secure sensitive data collaboration in Microsoft 365, GCC and GCC High.
eBook: Securing the Edge – Mastering Data Security in Defense
Defense organizations need a robust, adaptive solution that can keep pace with these dynamic threats and ensure sensitive data remains protected. This eBook explores the opportunities for enhanced data protection when you combine NC Protect with your existing Microsoft ecosystem and solutions like Microsoft Purview Information Protection.
Webinar: Extending Microsoft Collaboration Applications with ABAC for Enhanced Security and CMMC Compliance
Explore how archTIS's NC Protect implements a Zero Trust model for file access and sharing, ensuring compliance with CMMC and NIST standards to enable secure handling and collaboration on FCI and CUI.

NC Protect NIST 800-172 ABAC Capabilities Matrix
This Capabilities Matrix highlights how NC Protect provides the access control mechanisms defined in NIST SP 800-162 Guide to ABAC.
White Paper: Protecting Sensitive Data with Digital Security Watermarks
How to Secure Your Digital Assets with Automated Security Watermarks: Use Cases and Tools

White Paper: ITAR Compliance Checklist
A guide to compliance and information security requirements and best practices for achieving ITAR compliance.
Solution Brief: NIST SP 800-162 ABAC Model
Explore how NC Protect implements Attribute-Based Access Control (ABAC) capabilities following the NIST SP 800-162 ABAC model to enhance and complement your existing Microsoft security framework.

White Paper: CMMC 2.0 – Jumpstart FCI & CUI Protection with Data-Centric Zero Trust
Explore how extending a Zero Trust approach to file access and sharing ensures compliance with the CMMC 2.0 standards that map to NIST 800-171 and NIST 800-53 for secure and compliant collaboration of FCI and CUI.

eBook: The BYOK Gap in Microsoft Azure and M365
Understanding the potential risks of retaining encryption keys with Cloud Service Providers (CSP), including Microsoft Azure and Microsoft 365 (M365),
that can lead to data exposure and non-compliance with GDPR and other data protection laws.
No results found.
