Classified File Sharing & Document Collaboration
Secure Classified Information Collaboration with Kojensi

KOJENSI IS AN ACCREDITED CLASSIFIED FILE SHARING & DOCUMENT COLLABORATION SOFTWARE PLATFORM FOR DEFENCE, MILITARY AND GOVERNMENT





MILITARY-GRADE SENSITIVE & CLASSIFIED FILE SHARING & DOCUMENT COLLABORATION
For Defence, Intelligence, Government and Defence Industry Suppliers who need the ability to share sensitive and classified information internally, with partners and clients, Kojensi is a proven and accredited multi-level security (MLS) classified file sharing and document collaboration software platform. It enables productivity while managing the compliance and security of sensitive information. Unlike spending millions to build and manage your own classified information management system, Kojensi enables secure, compartmentalized collaboration out of the box for less time and money.
Compartmentalized File sharing & collaboration delivers sensitive information, quickly & Securely
Kojensi is a highly secure platform for the compartmentalized sharing and collaboration of classified information.
Accredited and hosted in a PROTECTED cloud and can be installed on-premises or in a private cloud.
With Kojensi SaaS you can be up and running within a day.
Uses a data-centric, zero trust security approach built on attribute based-access control (ABAC).
A file’s attributes, such as security classification, organisation and country reliability, determine who can access, edit and download files.
Ensures that sensitive and classified information is only accessible on a need-to-know basis.
Information custodians can easily configure file access, security and sharing settings with a user-friendly interface.
Create, co-author and share documents internally and with partners, fostering real-time collaboration.
Users can create a Community of Interest and invite new partners to join within minutes.
Five Eyes security models, classifications and mappings are preconfigured so you can start securely sharing instantly.
Explore Kojensi’s Key Capabilities
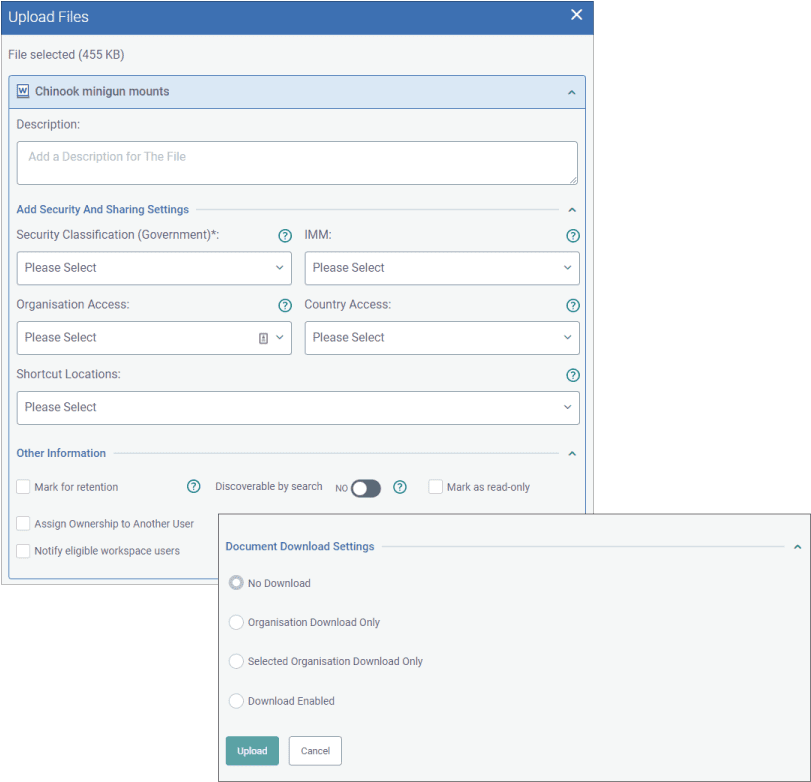
Control how your information is accessed and used
- Empower information custodians to effortlessly configure file access, security and sharing settings through a user-friendly interface.
- Data-centric, attribute-based access control (ABAC) policies determine who can access sensitive information.
- Access is controlled by user security level, organisation and country.
- Distributed administration provides complete control over information, with no super users.
- Control whether documents are private or discoverable in search, or whether viewers can see, edit or download information.
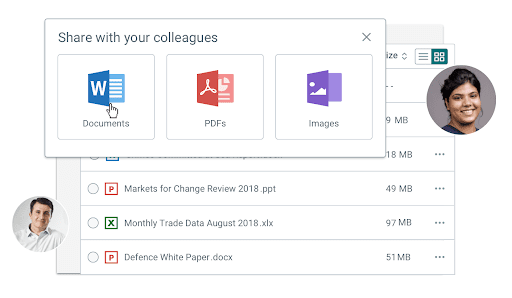
Securely share sensitive files, quickly and easily
- Easily set up a Community of Interest (COI) to allow people from multiple organizations to collaborate on information securely.
- Use secure workspaces to quickly and easily share any file type of up to 5GB internally or with partners.
- Share files including documents, spreadsheets, presentations, PDFs, images, CAD drawings, videos, etc.
- Control whether files can be downloaded, edited or only viewed inside of Kojensi.
- A full audit trail, version control, and tracking ensure transparency and assist with auditing requirements.
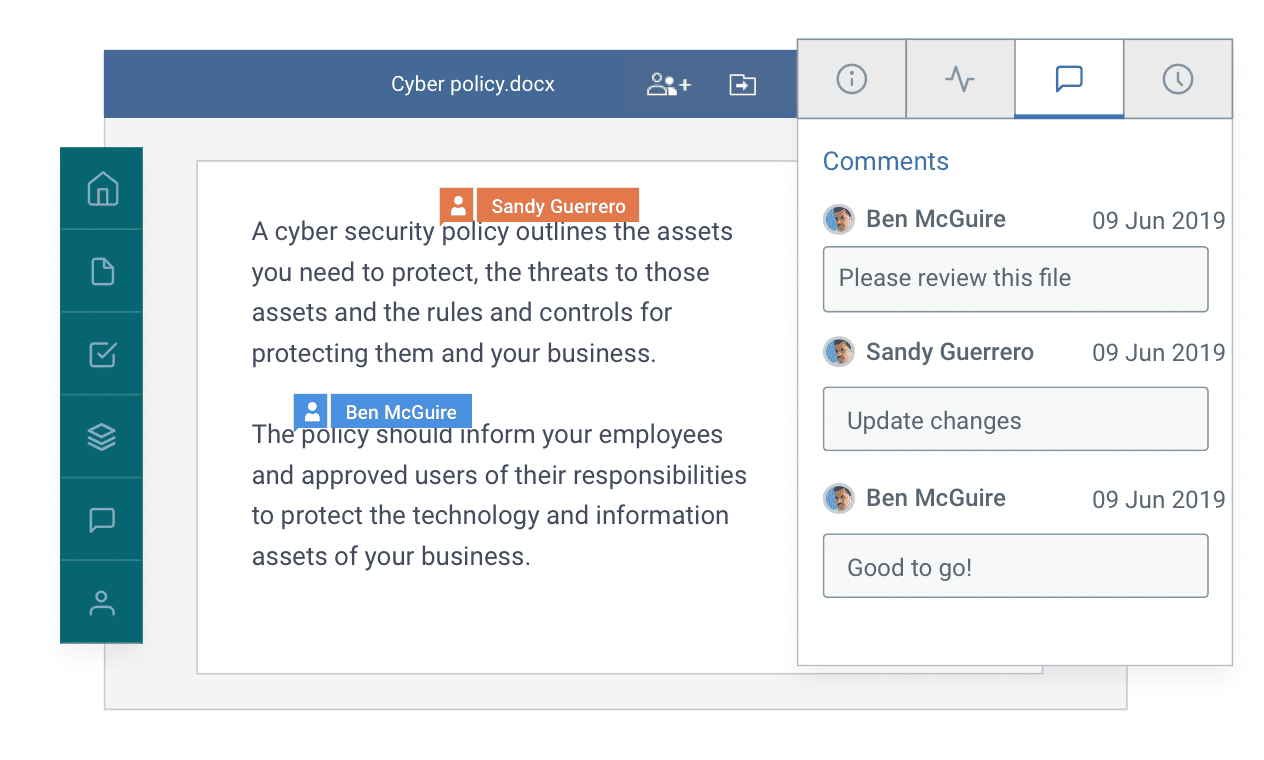
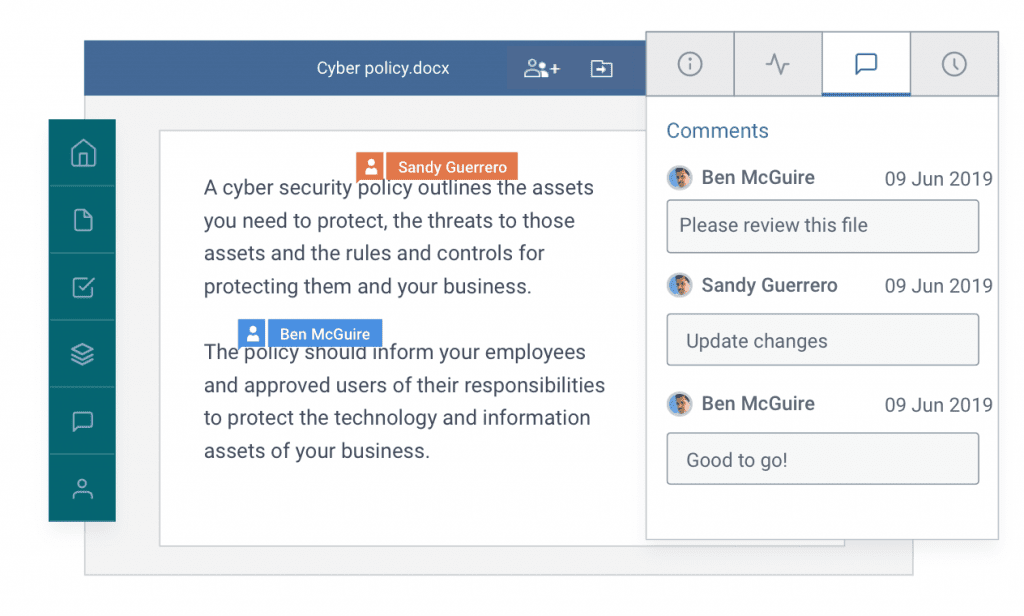
Individually edit documents or
co-author them in real-time
- Create, edit and co-author documents, spreadsheets, and presentations inside of Kojensi, tracking changes as you go.
- Co-author and collaborate on documents with multiple people in real-time.
- Leave comments or chat with co-authors in real-time while you work.
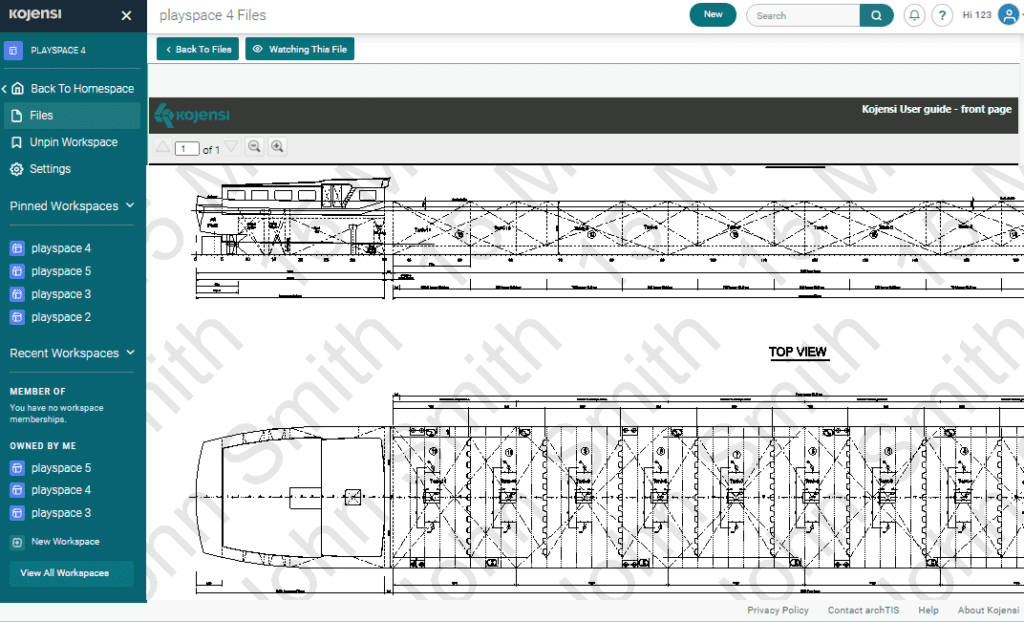
Secure Document Viewer
- An in-app Secure Document Viewer enforces read-only viewing of sensitive information for multiple file formats.
- Add a custom digital security watermark containing any user or file attributes to viewed documents for security and auditing purposes.
Increase productivity with collaboration tools
- Collaborate on documents, spreadsheets and presentations securely within the built-in editor.
- Stay up to date on work and projects with document version control, tasking and notifications.
- Leave comments on documents and files to inform colleagues and partners of suggested changes.
- Work together in real-time with secure co-authoring sessions and in-file chat.
- Collaborate with third parties using secure compartments without giving access to your whole environment.
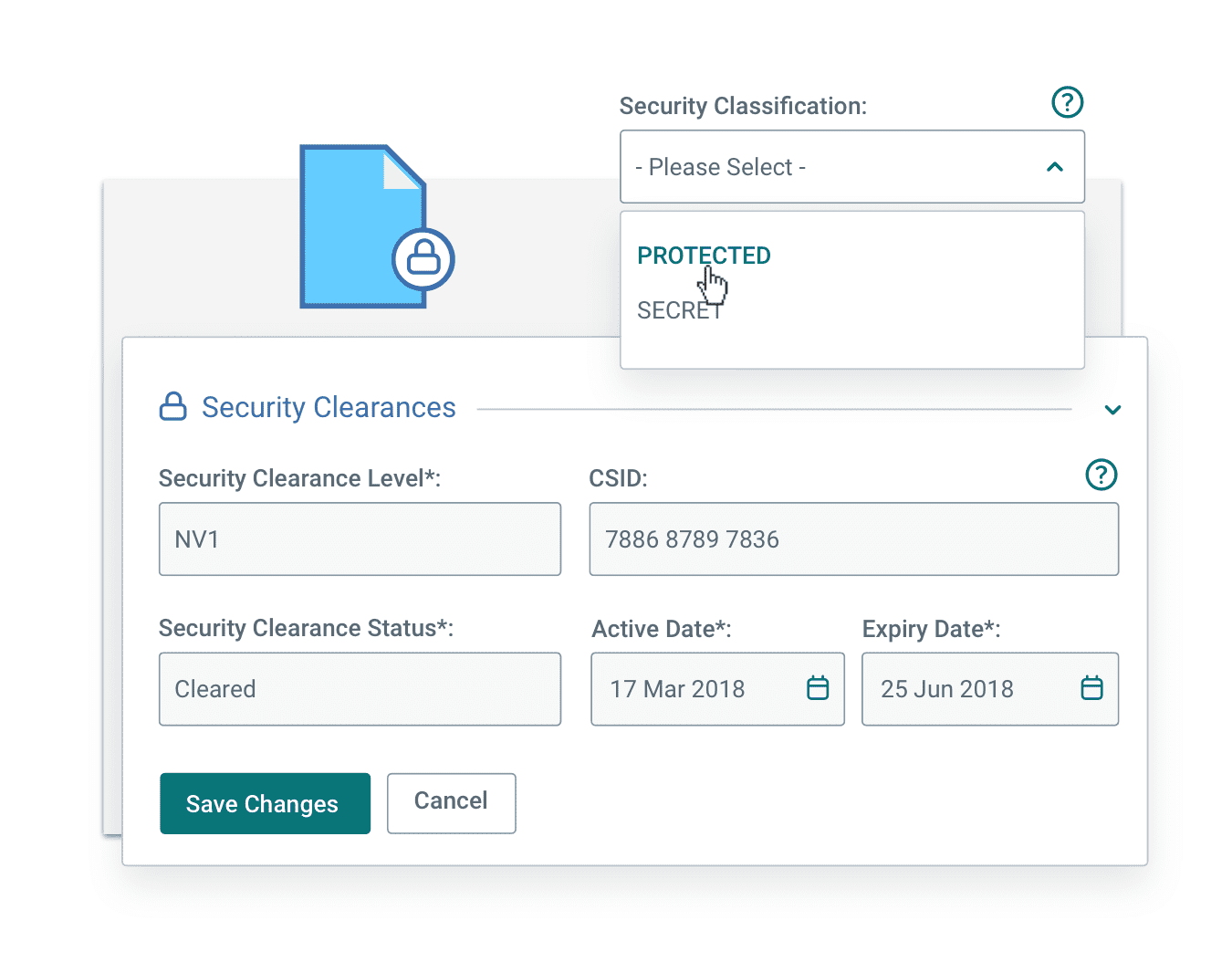
Ensure compliance with information security regulations
- Assists with meeting information security requirements for domestic and international Defence and Government regulations including DISP, PSPF, ISM and ITAR.
- Handle and manage information up to PROTECTED, in an ASD-certified PROTECTED cloud, or TOP SECRET, in a private cloud, on-premises or deployed environment.
- Support single sign-on (SSO) and multi-factor authentication (MFA).
- A full audit trail, version control, and tracking ensure transparency and assist with auditing requirements.
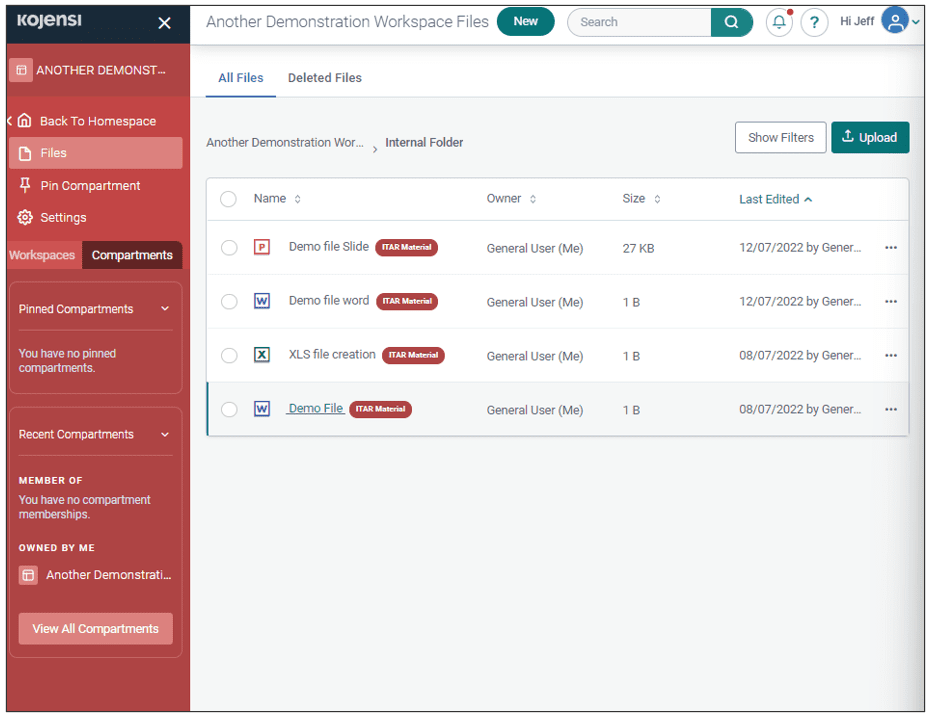
Export Control Compartments designed to make the management of restricted information easier
- Designed to quickly alert users of restricted export-controlled content.
- Additional User Access Control to ensure compliance.
- Extended Auditing Capability to assist with meeting governance and regulatory requirements.
One platform, three applications

Kojensi SAaS
Hosted in a PROTECTED cloud, the accredited Kojensi SaaS platform enables private and public sector organisations to share and collaborate on files in a secure space.

Kojensi Enterprise
Deployed on-premises or in a private cloud, Kojensi Enterprise enables multi-level, multi-coalition and multi-domain collaboration of information classified up to TOP SECRET.

Kojensi Field
Capable of being deployed on ruggedised equipment, Kojensi Field allows military, government, aid and emergency service workers to collaborate in the field.
Frequently Asked Questions
How does Kojensi differ to other products?
Security controls ensure the end user is the custodian of their own data
Kojensi enables users to set rules for access to files and documents, including the security classification, organisation name, and country. Users can only see or access a document or file if they meet the rules set for the document. Users can also set the level of read/write access others can have on workspaces and documents.
Secure co-authoring of sensitive and classified documents
Kojensi allows users to co-author sensitive and classified files, including documents, spreadsheets and presentations. Organisations can use Kojensi to share and co-author documents up to PROTECTED in an accredited cloud-based application or higher-level documents in an on-premises or private cloud solution.
Distributed administration saves users time and reduces administrative overhead
There are no super users inside of Kojensi, users have complete control and visibility over the documents and files they contribute. Each user is able to set up secure Workspaces and decide the security controls and levels applied to both Workspaces and individual documents. This saves users time empowering them to get started and work straight away.
Is Kojensi only limited to Documents, Spreadsheets and Presentations?
There are no limits to the type of file users can share using Kojensi. This means that any file can be shared securely, for example:
- Videos
- Images
- CAD drawings
- PDFs
- Documents
- Spreadsheets
- Presentations
The built-in editor only supports file creation and co-authoring for documents, spreadsheets and presentations.
Can Kojensi be used for Export Controlled information?
Kojensi’s Export Control Compartments make the management of regulated export data easier. These Compartments allow users to quickly identify Export Controlled information (e.g., ITAR, DEC) and enable content owners to apply the appropriate security tags from a simple-to-use interface. The simplified creation, management and enhanced auditing of the compartments enables Export Control Managers to streamline the business process for meeting compliance requirements.
Does Kojensi support external guest users?
With Kojensi you can invite guest users from any organisation to collaborate on and share files in a highly secure compartmentalized environment. It is perfect for use within and between Government, Defence, Industry, Universities, and other third parties. Kojensi provides all of your stakeholders with a secure place to collaborate while ensuring users can only access authorized information.
What makes Kojensi more secure than other file sharing platforms?
Kojensi uses a security methodology called Attribute Based Access Control (ABAC), which enables users to have fine-grained control over how information is shared and accessed. Attributes (e.g., security classification, organisation name and country) can be added to documents and files, giving the information owner strict control over who accesses it.
Is Kojensi SaaS IRAP Assessed and Accredited?
Is Kojensi SaaS IRAP Assessed?
The Information Security Registered Assessor Program (IRAP) is a comprehensive independent Cyber assessment program designed to evaluate a system’s security posture against the Australian government’s security policies and guidelines, including the Protective Security Policy Framework (PSPF) and the Information Security Manual (ISM).
The IRAP assessment is recognised by the Australian Government and demonstrates archTIS’ commitment to meeting the stringent government security and compliance required to deliver a secure, trusted collaboration platform to safeguard our clients’ data. IRAP reports are commonly used as a foundation for certification and accreditation of Australian Government systems under the PSPF (guidance here). Further to this, guidance has been launched to address specific considerations for a Cloud Services Provider (CSP).
The IRAP report provides detailed information on security risks and controls evaluated through the assessment and identifies any areas of concern or focus that should be considered by a security accreditation authority. archTIS uses this to drive our security improvement program of work. An IRAP assessment is not a right to operate, however the evaluation provides significant coverage of key information and technology risks that would enable security authorities to authorise the capability to operate across PROTECTED data.
Kojensi completed its first IRAP assessment in 2019 against PROTECTED ISM security controls. archTIS has recently completed its second full IRAP assessment (including latest ISM controls, Essential 8 and incorporation of Cloud Service Provider changes). archTIS engaged an independent third-party IRAP assessor to evaluate the Kojensi SaaS platform, the report has noted the significant improvements in overall security posture since the last evaluation. In parallel, the Kojensi IaaS cloud hosting provider (Vault) has recently completed their latest full IRAP assessment which has also been considered as part of the Kojensi IRAP report.
Is Kojensi SaaS Accredited?
The Kojensi SaaS platform is accredited by the Australian Federal Government at PROTECTED.
Each Australian Government organisation will be required to consider accreditation of the capability for their use, however the IRAP assessment and OGA accreditation can be leveraged to accelerate this process. archTIS has a significant amount of security accreditation supporting material that can be shared with customers to accelerate these activities.
Where can I find out more?
Contact your archTIS sales representative to request the IRAP report and specific accreditation information.
Experience Kojensi. Request a Demo.
See how we enable secure, compartmentalized classified document collaboration and sharing.
