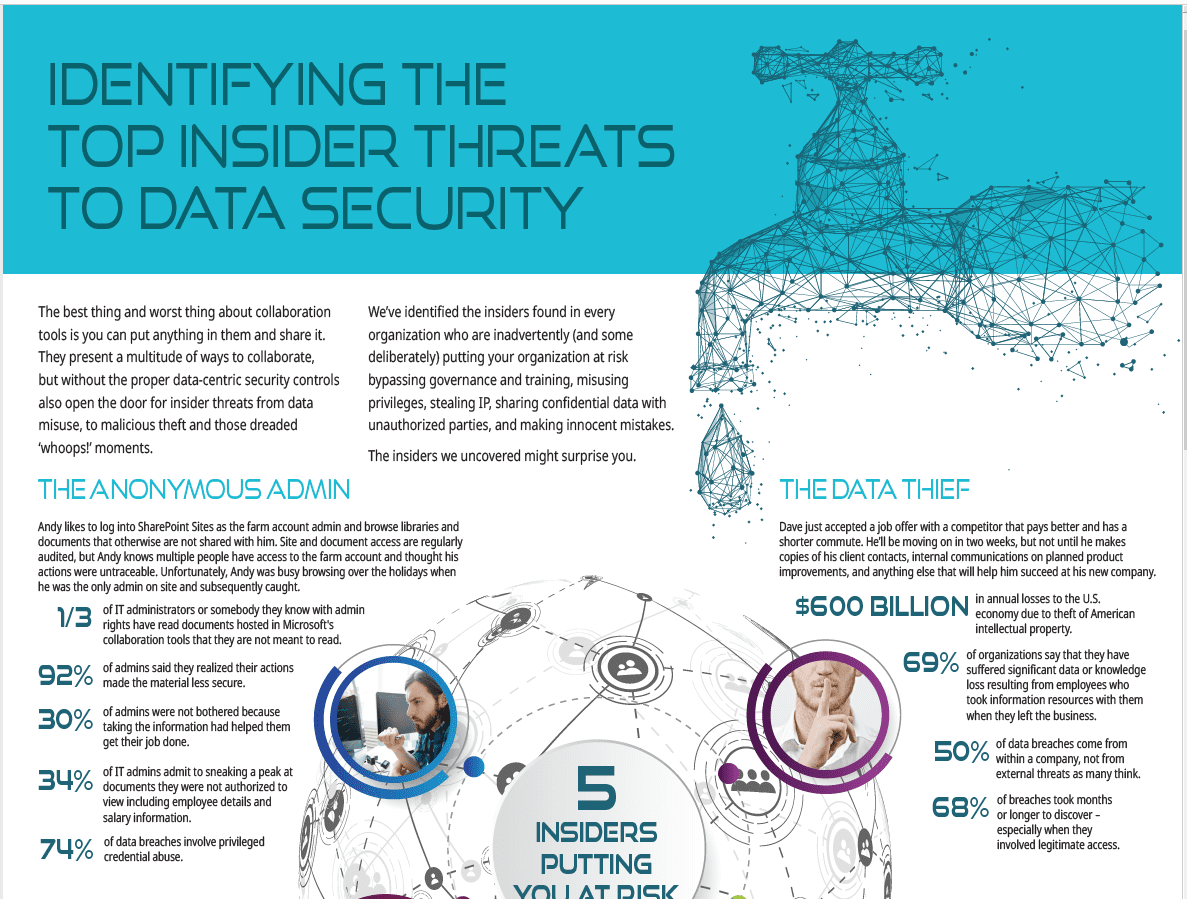
Identifying The Top Insider Threats to Data Security
The best thing and worst thing about collaboration tools is you can put anything in them and share it. They present a multitude of ways to collaborate, but without the proper data-centric security controls also open the door for insider threats from data misuse, to malicious theft and those dreaded ‘whoops!’ moments.
We’ve identified the insiders found in every organization who are inadvertently (and some deliberately) putting your organization at risk bypassing governance and training, misusing privileges, stealing IP, sharing confidential data with unauthorized parties, and making innocent mistakes. The insiders we uncovered might surprise you.
Here’s a sneak peek at just one of the characters we uncover in our new Infographic.
The Anonymous Admin
Andy likes to log into SharePoint Sites as the farm account admin and browse libraries and documents that otherwise are not shared with him. Site and document access are regularly audited, but Andy knows multiple people have access to the farm account and thought his actions were untraceable. Unfortunately, Andy was busy browsing over the holidays when he was the only admin on site and subsequently caught.
- 1/3 of IT administrators or somebody they know with admin rights have read documents hosted in Microsoft’s collaboration tools that they are not meant to read.
- 92% of admins said they realized their actions made the material less secure.
- 30% of admins were not bothered because taking the information had helped them get their job done.
- 34% of IT admins admit to sneaking a peak at documents they were not authorized to view including employee details and salary information.
- 74% of data breaches involve privileged credential abuse.
4 Other Insiders Putting You at Risk
Meet the 4 other insiders putting your organization at risk, and learn the 4 things you can do to prevent insider breaches.